Ace Tips About How To Prevent Buffer Overflow

Pay close attention when checking for boundaries and make sure you stop at the correct length.
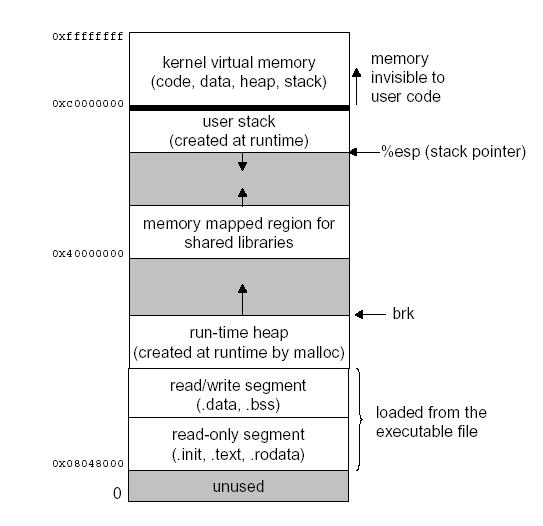
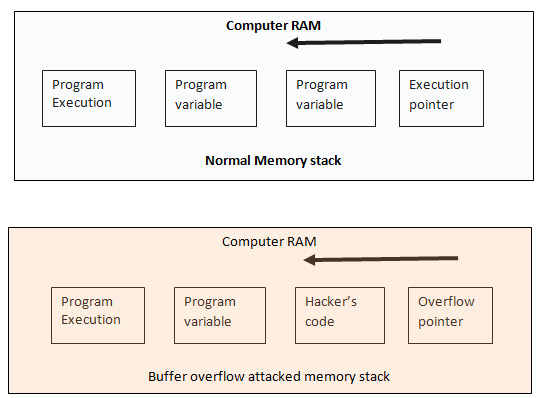
How to prevent buffer overflow. Buffer overflow attacks typically need to know where executable code is. Putting the desired code to the target program, 2. While checking for bugs and opting for automatic language.
#include <stdlib.h> #include <string.h> int main (int argc, char *argv []) { char *unsafe_string = hello,. Use strnlen and check for malloc success, like so. Using fgets instead of scanf helps prevent buffer overflow in our example.
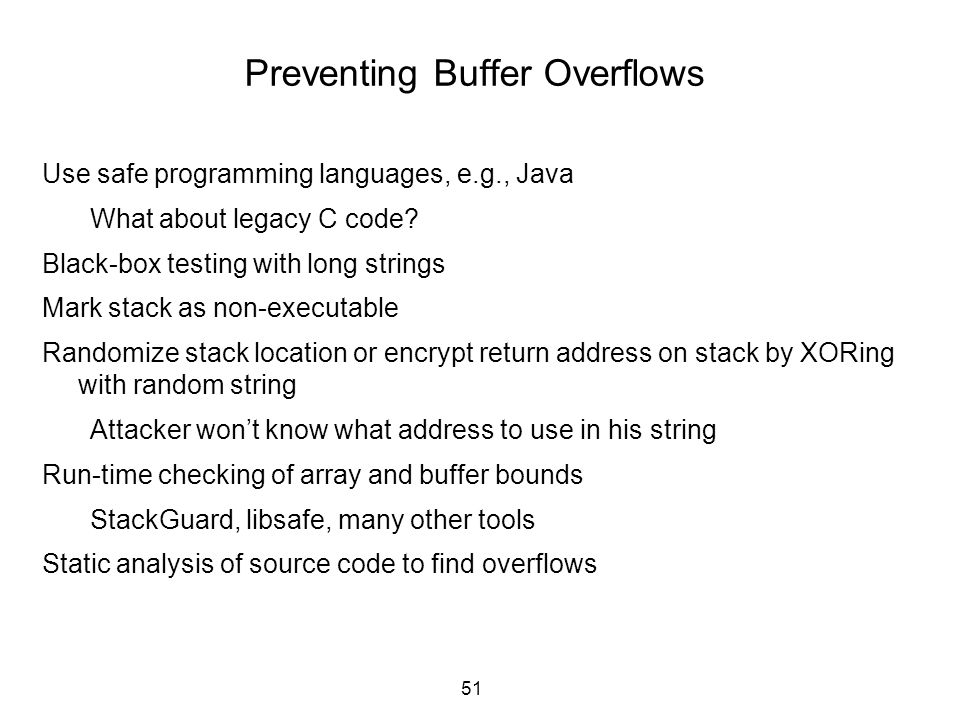
To bulk up enterprise defenses, ensure secure coding practices, and prevent buffer overflow vulnerabilities by adhering to the following: This includes common protection like: How to avoid buffer overflow.
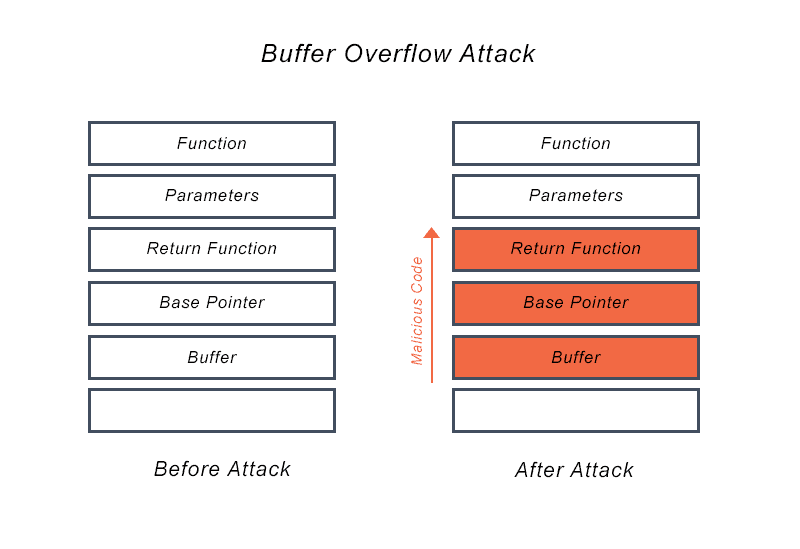
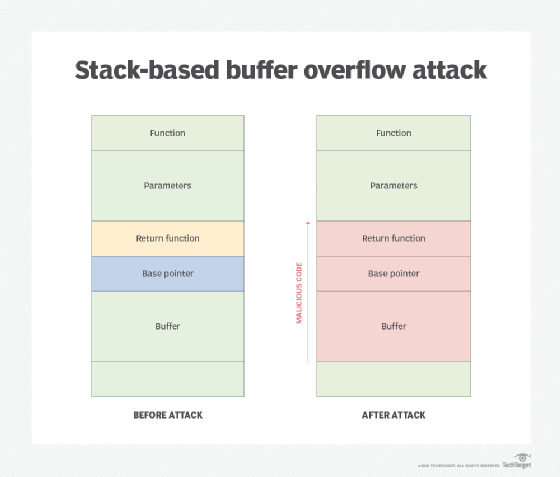
To prevent buffer overflow exploits, it is necessary to understand how they occur. Through the use of safe buffer handling functions and appropriate security features of the compiler and operating system, a solid defense against buffer overflows can be built. Avoid using functions which don't perform buffer checks (for.
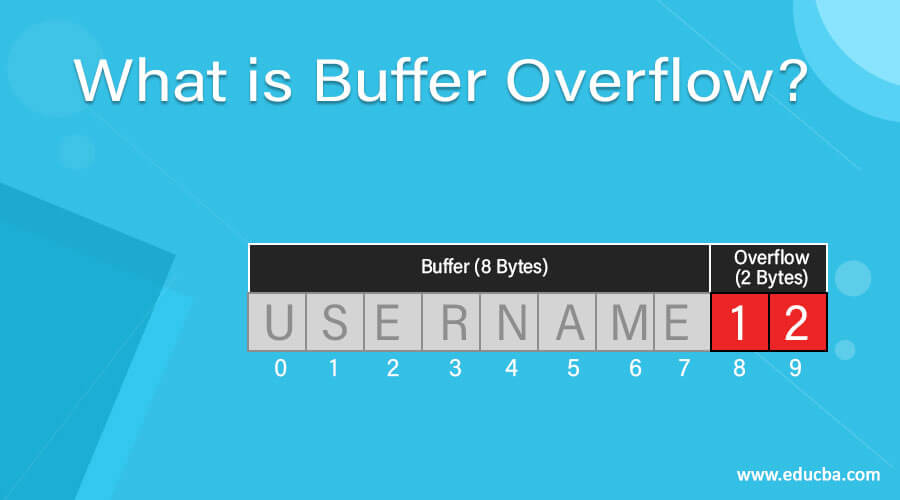
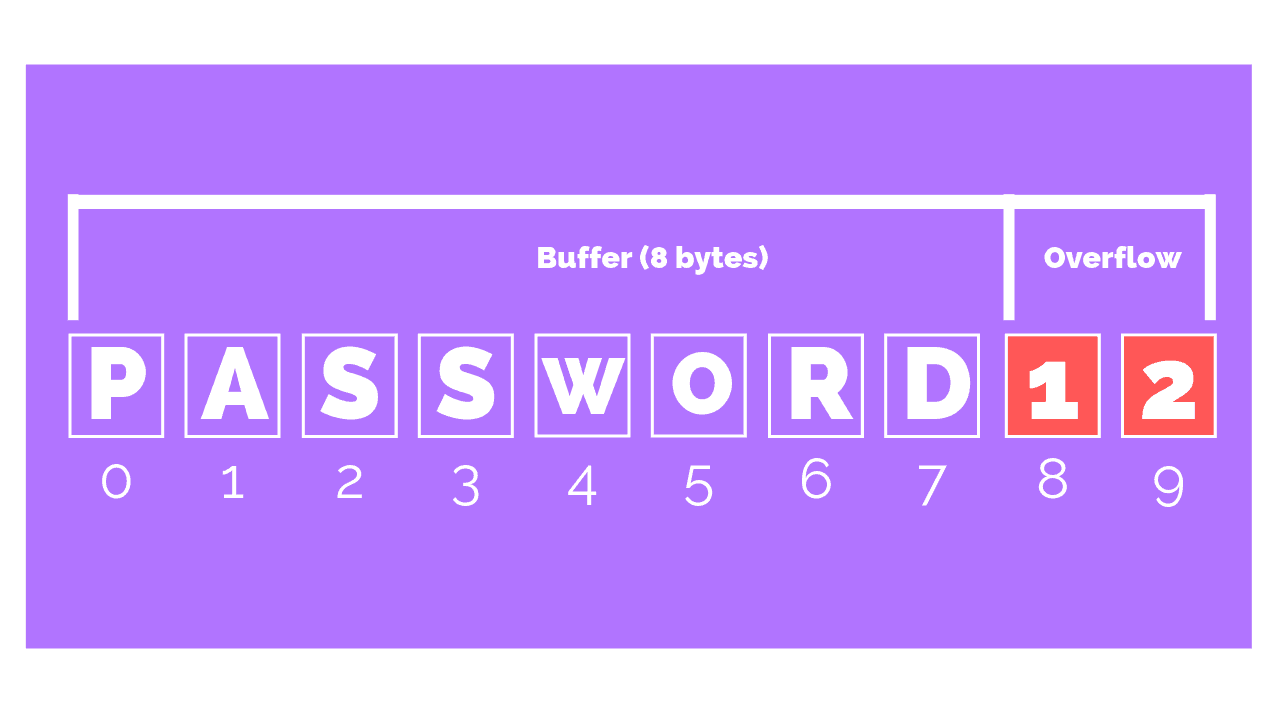
When programs are written in languages that are susceptible to buffer overflow vulnerabilities,. A possible solution is to use a sentinel value to represent the end of an array. The actual buffer overflow by copying more data in.
How to mitigate buffer overflows use an interpreted language which isn't susceptible to these issues. Summarizing, we can say that a buffer overflow attack usually consists of three parts: Writing secure code is the best way to prevent buffer overflow vulnerabilities.
Make buffer overflow prevention part of your devops process kiuwan code security integrates with leading ci/cd tools so that you can take a devops approach to buffer overflow. For example, you could define the interface such that.member == 0 if and only if that is the.